You are a celebrity (to hackers)
If you have an account online, hackers will try to get into it and access your data – either in the attempt to expose you, steal from you, or embarrass you. Also, no, the above GIF does not actually show how hacking is done.
Oh, you are not a celebrity? Statistically, you are also a target. Bill Laberis of Securityintelligence.com stated in November 2016, “According to the Identity Theft Resource Center’s (ITRC) “ITRC Data Breach Report,” more than 29 million records were exposed in 858 publicized breaches across sectors including financial, government, healthcare, and education.”
Scary? Sure.
Should we be worried? For now, yes.
If governments and private institutions that have your sensitive data do not match up to the level of hackers, we will be in trouble. Laberis also stated, “Only 38 percent of organizations surveyed for ISACA’s “2015 Global Cybersecurity Status Report” believed they were prepared to meet the onslaught of sophisticated cybercrime.”
However, we CAN protect some of our data from being revealed in these attacks.
1) Know where and how you are vulnerable

Dick Costolo, Jack Dorsey, Evan Williams and Biz Stone (Photo by Andrew Burton/Getty Images)
The following is a list of executives:
- Sundar Pichai, CEO, Google
- Travis Kalanick, ex-CEO, Uber
- Jack Dorsey, CEO, Twitter & Square
- Dick Costolo, ex-CEO, Twitter
- Evan Williams, ex-CEO, Twitter
- Biz Stone, co-Founder, Twitter
Do you know what they have in common? Their Twitter accounts were hacked.
Yes, that list includes 4 Twitter executives – you did not read that wrong.
However, what truly makes these executives related is that the hackers were able to maneuver their way into their Twitter accounts because they were linked to third party websites – Pinterest, Quora, and FourSquare specifically.
The fact that this happened shows that accounts can easily be accessed if they are linked to others. The more linked accounts, the more likely one of them is to be penetrated.
I checked my vulnerability through MyPermissions, and it showed me that I have 145 apps connected to my Facebook and Instagram accounts. That is crazy, I know. I plan on disconnecting my information from third-party apps I no longer use.
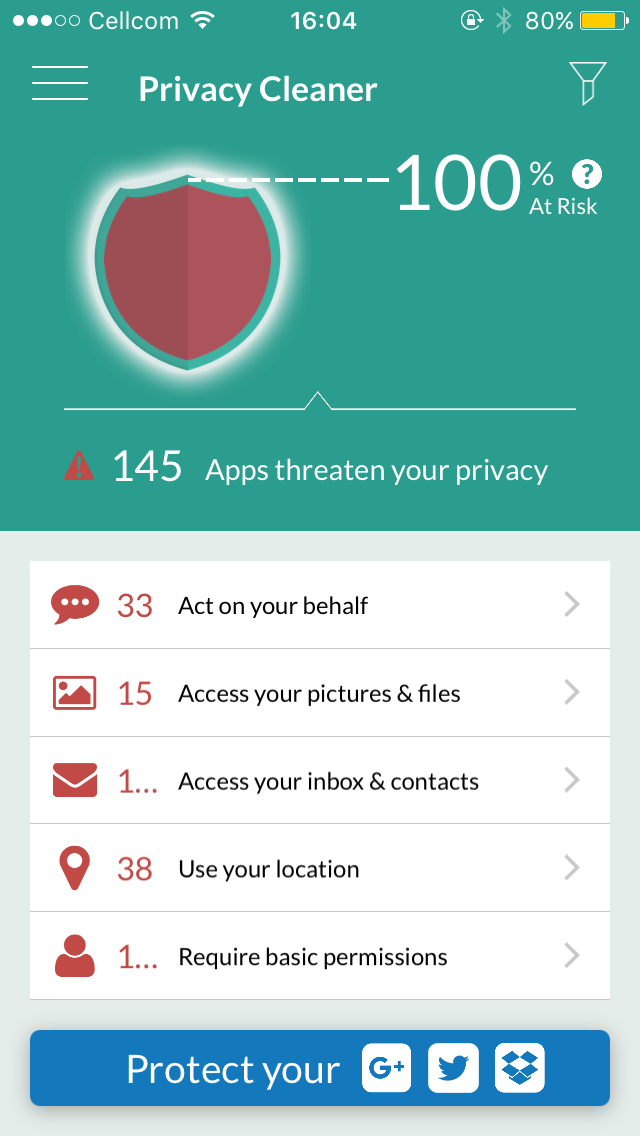
Screenshot of my MyPermissions screen. With MyPermissions I can make sure my data is safe by removing my information from third party apps I no longer use.
2) Be mindful of where you save your private info

Lawrence’s iCloud was hacked. (Photo: Jason Merritt) Source: Getty Images
On August 31, 2014, a collection of almost 500 private pictures of celebrities were posted on 4chan by hackers. The stars included Miley Cyrus, Scarlett Johansson, and Vanessa Hudgens.
The hackers were able to get their images via their Apple iCloud account – iCloud saves all photos, notes, contacts, and emails on Apple devices into Apple’s cloud. Although the pictures can only be accessed with a username and password, the flaw was that the password could be guessed an unlimited amount of times.
Why is something that happened three years ago relevant today?
It reminds us that we should be mindful of what we put in cloud-based storage systems. Logically, it is a lot easier to access something if it can be accessed from anywhere. It is a lot harder to access something if it is in one secure place.
To keep your photos safe, disengage the cloud settings from your device, or at least ask yourself “Would I want everyone to see this?” when saving to the cloud.
from the movie “Sex Tape” via GIPHY
The Bottom Line
Using these two tips will surely protect people from hacking scares. If it can happen to influential executives and celebrities, then it could easily happen to us.